3-ALARM TECHNOLOGY
In the world of anti-theft systems, a dangerous misconception persists: many believe that a high-quality jammer is all it takes to become invisible to any security system. Reality is far more hostile. A jammer is a tool designed to manipulate the gates (pedestals) by disrupting their processing logic. Но what happens when your adversary isn't the gate, but the sensor itself attached to the merchandise?
This is where we enter the territory of 3-Alarm technology. This class of devices doesn't just hang passively on a garment; they are equipped with active electronics capable of "listening" to the environment and independently initiating an alarm.
Evolution of Defense: From 1 to 3
To neutralize these threats, you must clearly distinguish sensor types by their functionality:
1-Alarm (Standard):
! Classic passive tag.
- No battery. Acts strictly as a signal reflector. If you pass through the pedestals, the gates "see" the tag and the gates themselves alarm. If you cut the lanyard—nothing happens.
2-Alarm (Tamper Protection):
! Equipped with a battery and a security circuit. Includes most spiders, cable tags, etc.
- Function: If the gate sees the tag—the gate alarms.
- Bonus: If the cable is cut (continuity is broken)—the tag itself begins to scream. However, if removed in a booster bag or with a jammer, it remains silent (as it does not react to the gate's field).
3-Alarm (Active Protection):
! The apex of retail paranoia.
- Function 1: Gates see the tag—gates alarm.
- Function 2: Cut the cable—tag alarms.
- Function 3 (Critical): The tag features an integrated receiver. If it "hears" the specific gate signal (AM or RF), it activates its internal siren.
The Problem
A jammer suppresses the gate's receiver, but it cannot "turn off" the signal that the gate transmits. A 3-Alarm tag, when near the pedestals, detects their powerful emission and begins to scream even if the gates themselves are "blinded" by your jammer.
Technical Architecture
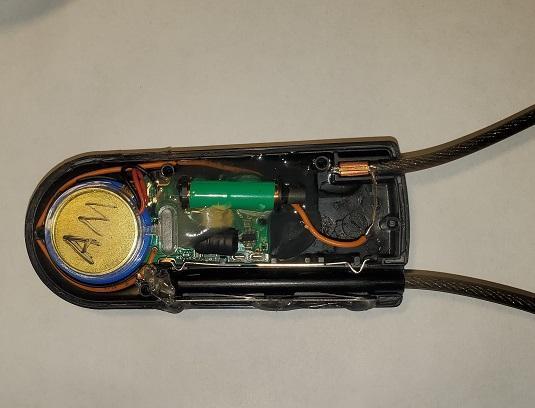
Inside a 3-Alarm tag (whether it's a "spider" or a hard tag) lies more than just a ferrite core coil. It houses a microchip analyzer, constantly powered by a battery.
The electronics continuously scan the airwaves via an internal antenna. The analyzer's firmware looks for specific signatures—pulse periods characteristic of EAS systems (58 kHz for AM or 8.2 MHz for RF). Once the tag recognizes this "handshake" (upon approaching the pedestals), it activates the built-in piezo speaker and LED.
Primary Manufacturers:
- Alpha Security: The market leader. Usually marked with the "3-alarm" logo. Frequently seen as "spiders" and CableLok tags.
- Century and WG (4-alarm): Utilize similar technologies, often without external marking, making identification difficult.
Crucial Detail: Post-detachment behavior varies. With Alpha Security and Century, the 3-Alarm function is typically deactivated when the lock is opened. In other models (especially older or specific spiders), the electronics may remain active even in the open state.
Countermeasures: Diagnostics and Bypassing
Since visually distinguishing 3-Alarm from 2-Alarm can be difficult—especially with brands that omit markings—we have developed several tactical approaches.
1. Electronic Diagnosis (Feature of our devices)
We have integrated a "Gate Signal Emulation" function into our hardware.
Operation: In a safe location (fitting room or deep within the store), activate this mode on your jammer and bring it close to the suspicious tag.
Result: The jammer generates a weak but precise gate signal pattern. If the tag has 3-Alarm functionality, it will "hear" it and begin to beep or flash in your hands.
Conclusion: If the tag reacts to the emulation, you cannot pass through the gates even with a jammer active. If there is no reaction, the path is clear.
2. Physics vs. Electronics (Magnetic Saturation)
This method relies on the physical properties of ferrite and is effective when you cannot or will not remove the tag but MUST extract the item.
- Theory: The tag's antenna is wound around a ferrite rod. Ferrite amplifies signals, but only up to a specific saturation limit. When placed in a powerful magnetic field, ferrite loses its properties—it becomes "blind."
- Practice: Use a high-powered magnetic detacher. By applying it to the tag's chassis where the ferrite coil is located (usually the side furthest from the lock), the tag stops perceiving the gate signals. The coil loses inductance, and the electronics "think" they are in a silent environment.
Deep Dive: Sensormatic SuperTag 3T
Consider one of the most sophisticated examples—the SuperTag 3-Tone Alarming (3T). This is a modification of the legendary SuperTag, upgraded with "brains" and a battery.
 Sensormatic SuperTag 3T
Sensormatic SuperTag 3TDefense Mechanisms:
- Pin Circuit: The needle is part of the electrical circuit. If the needle is clipped or forcibly ripped out—the circuit breaks, triggering the alarm. However, if the lock is opened with a hook detacher, a specific internal mechanism presses a contact pad, legally breaking the circuit without an alarm.
- Field Detection: The internal AM coil listens for the 58 kHz frequency. Detecting it triggers the siren.
Operational Procedures (Professional Approach):
Use a standard Sensormatic hook. Insert the hook, engage the mechanism, and extract the pin. If you intend to leave the tag in the store, re-insert the pin. It will remain silent.
Insert the hook. Firmly cover the tag's speaker with your hand (to muffle the sound). Extract the pin, then pull the hook out *without the pin inserted*. The tag will emit a short "BEEP" and deactivate its security system. It is now a dormant piece of plastic that can be carried out like a standard 1-alarm tag.
As described above, a powerful magnet applied to the ferrite zone (opposite the hook aperture) drives the core into saturation. The tag becomes "deaf" to the gates and will not trigger during exit.
What NOT to Do
Barbaric methods, such as crushing the casing with pliers, are unprofessional. They create noise, leave evidence, ruin the merchandise, and if caught, qualify as intentional property damage, escalating legal consequences. However, we don't live in a world of fairy tales—if no other option exists and the target is critical, study the internal layout carefully and act decisively.
Knowledge of the technology is your primary advantage. 3-Alarm sensors are designed to intimidate amateurs. For those who understand the physics, it is merely a device with predictable logic that can be bypassed.