THE HISTORY OF EVOLUTION
My dream is for everyone who comes to me to realize one simple truth: no one except me and the team I have assembled is engaged in actual technological development for you.
This text is not a promotional brochure. It is a documentary record of the path taken since the days when EAS gates were "dumb", and the methods to bypass them were primitive. I want you to understand what you are working with, and why professional hardware cannot be a "magic wand".
In a world where security systems update faster than consumer electronics, remaining in the shadows and at the bleeding edge of progress for over fifteen years is not just an indicator of stability. It is the result of deep engineering evolution and personal necessity.
The main conflict of our movement today is the collision of real professional tools with the infantile myth of the "one-button solution." The market is overflowing with "snake oil salesmen" who exploit the human desire to get everything at once. They offer "2-in-1" devices with the logic: flip a switch — and everything around shuts down. They assure you there is no difference between AM and RF systems, and that primitive white noise is capable of deceiving the modern computer inside the EAS gates.
THIS IS A FUNDAMENTAL DELUSION.
There is no universal skeleton key for all locks. You don't try to pour diesel into a gasoline engine just because it is "also fuel," do you? Similarly, you cannot jam modern digital systems with adaptive filtering using archaic noise generators.
But to understand why we arrived at complex algorithms and modes, we must look back — to where it all began.
How the Legends Were Born
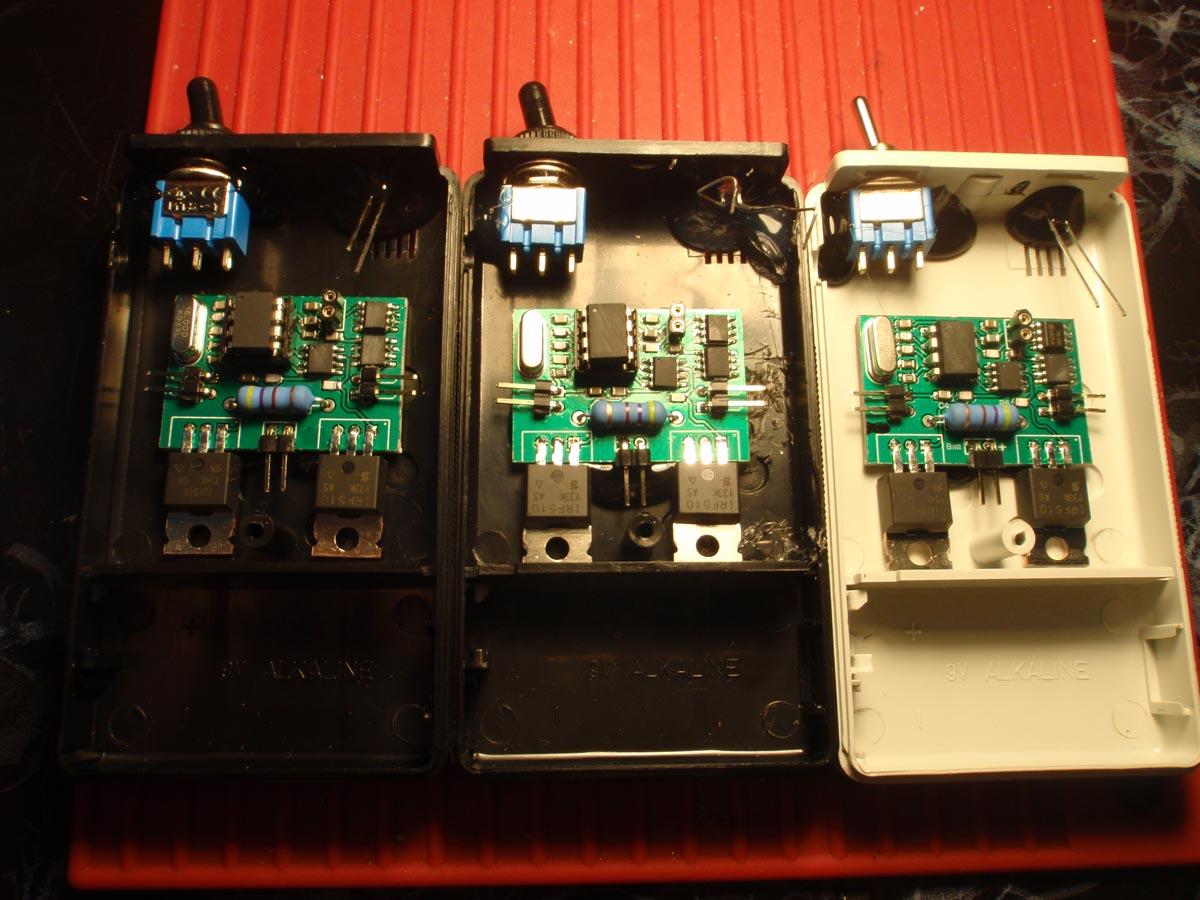
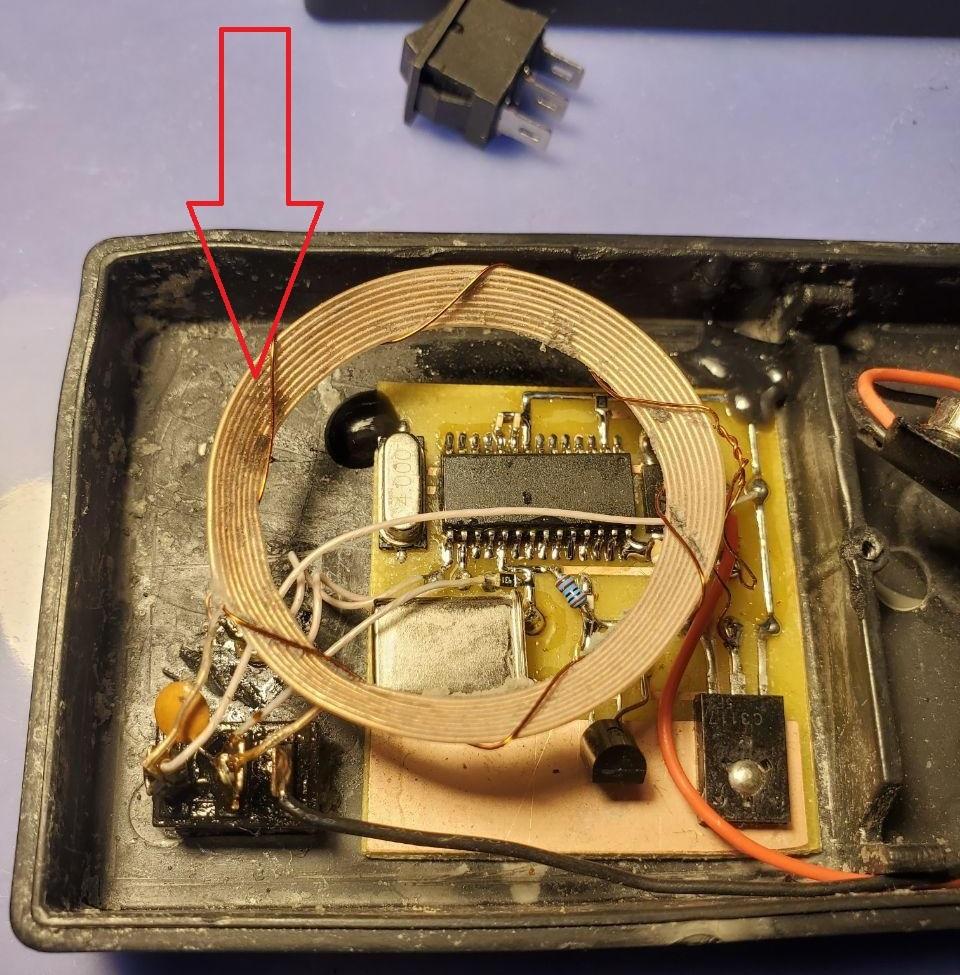
Information about the very first jammers surfaced around 2005–2007. Some amateur electronics enthusiast created an elementary noise generator on the exact frequency the EAS gates use to analyze the signal (58 kHz). The Internet was not yet saturated with specialized forums on our subject, and the creator's name remained lost to legend.
But years later, thanks to connections with hundreds of operators across the globe, one of those very first jammers fell into my hands.
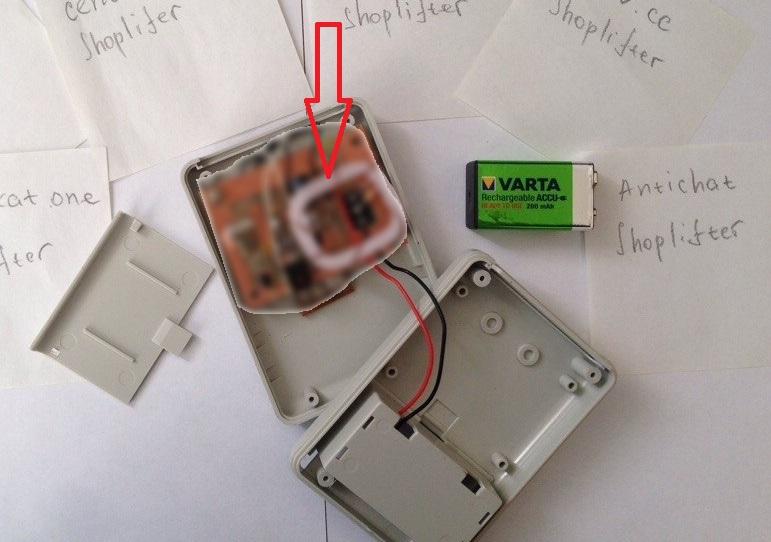
It was a simple black box powered by a 9V battery, utilizing the most crude solutions, lacking an optimized antenna and complex components. Very weak, but probably highly effective when interacting with the earliest, analog AM systems.
Around 2008–2009, intel surfaced about a similar device from Poland. The same weak generator, but with an external toggle switch. It was claimed to implement both AM and RF simultaneously. However, upon holding this device, it became clear: the RF power output was absolutely pathetic. Operators tried to work with it, but constantly complained about the lack of power and the fact that a bunch of EAS gates simply triggered alarms in response to it.
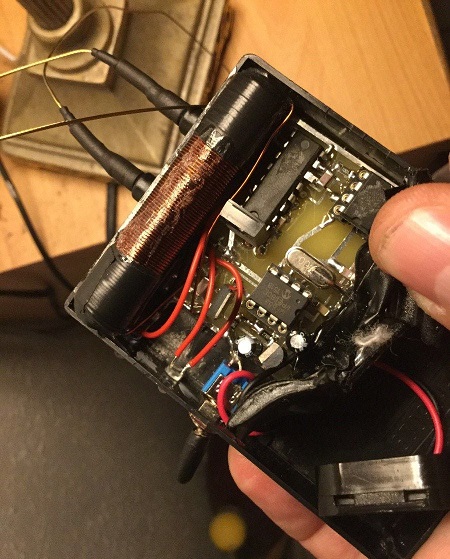
A few years later, a developer from Bulgaria stepped into the public eye. As he personally told me during Skype calls, prior to retirement, he was an employee of an EAS anti-theft company, and afterward — decided to turn it into a hobby.
In my opinion, this was the only device worthy of attention in all those years. It had sufficient power for 58 kHz, and the 8.2 MHz range was pulled off via an external antenna. But flawed algorithms, poor optimization, massive battery drain, and, most importantly, its exterior appearance made it extremely far from ideal for a professional.
No, I am not saying it was impossible to work with. I bought it myself for 1100 euros in 2010. It paid for itself, yes. But the constant issues were unacceptable to me.
With it came a wild paranoia: if you were randomly stopped and this was found, the sheer appearance of the device (buttons, toggles, wires) would trigger colossal problems. Ultimately, in 2012, I decided to get rid of it.
During this same period (2010–2012), a dozen makeshift devices passed through my hands. Operators sent me this garbage for trade, knowing I was hunting for ideas. These boxes were built strictly for a quick buck: minimal power, primitive soldering — outright shit that was simply dangerous to take into the field.
In 2011, on a forum where I was selling my hardware (detachers and shielding fabric), a character under the nickname Danko appeared. He started selling the most basic AM jammer for $200.
Finally seeing a Russian developer you could communicate with normally, I started supporting him. I helped with sales, tested new ideas in the real field (I was actively working stores myself back then and was the ideal field tester). Here is his best device from that period — a makeshift rig mounted inside a standard cigarette pack:
But a year passed, and there was zero progress. I started getting frustrated and soon uncovered the truth: Danko was not a developer at all. He simply acquired the schematic from a Belarusian guy who built automotive code grabbers, while Danko himself understood absolutely nothing about our niche.
The Point of No Return: The Guy from Yaroslavl and the Exile
Talking with clients, I learned of another developer from Yaroslavl (200 km from me). I contacted him and bought his device — it was advertised as a "2-in-1" for AM and EM (electromagnetic) gates.
The result? It jammed EM gates disgustingly and dangerously, AM — tolerably, but operated on a weak battery for a ridiculously short time. I applied basic knowledge from the past, resoldered the power supply for heavy-duty batteries, boosted the device, played around with it, realized I didn't need it, and sold it on that same forum.
Finding out about this, Danko went ballistic. Sensing trouble and seeing me as a competitor, he publicly accused me of stealing his "technologies" and organized a brutal witch hunt on the forum. The outcome — I was banned and permanently exiled.
If I hadn't been exiled then, I probably would have kept waiting for a "miracle inventor." But many of my contacts were severed, the sales platform destroyed, 20 pages of flawless reviews wiped out. And I needed jammers myself, my friends needed them, and the word-of-mouth demand hadn't disappeared. I couldn't send operators to the man who betrayed me.
I accepted the reality: the rescue of drowning men is the drowning men's own job.
The Birth of Technology and the Evolution of Camouflage (2012–2014)
I built my own website, without a forum, just a product list, and dove headfirst into engineering a device that had to be superior to everything in existence.
For several weeks, I gathered all my knowledge, contacted people from the technical university I attended, and spoke with my former academic advisor. Tuning these individuals to work in our "specific" sector was tough, but I managed it.
Two months later, I was able to supply my crew with high-quality hardware. It was a $300 AM jammer that matched the 1100-euro Bulgarian unit in every metric. RF systems didn't bother me much back then, as we already had excellent booster bags that solved most radio frequency issues.
We started selling devices housed in various everyday objects. These included:
- Flashlights.
- Blood pressure monitors.
- Portable hard drives (an absolute hit in Europe and the USA).
- Ultrasonic dog repellers (a hit in Russia).
For myself, I exclusively built bare-board setups. Wrapped in electrical tape or leather, they were as compact as physically possible. I didn't give a damn what it looked like, as long as it rested in a hidden pocket and saved my ass.
Simultaneously, EAS gates started getting smarter...
Early analog gates were so vulnerable that the impact of our jammers could cause them to simply freeze, go into a boot loop, or break entirely. A technician had to be called. This attracted unnecessary heat.
Gate manufacturers (Sensormatic, CrossPoint) began shifting to Digital Signal Processing (DSP). EAS gates ceased to be mere antennas — they became computers. They learned to filter out basic "white noise." The era of dumb jammers had come to an end. We began searching for new algorithms to not just make noise, but to inject mathematically precise errors into the gates' logic.
Forum Hustlers and the Illusion of a Pretty Wrapper
While we were grinding on new algorithms, what I call the "sucker-fleecing business" bloomed wildly across the Internet.
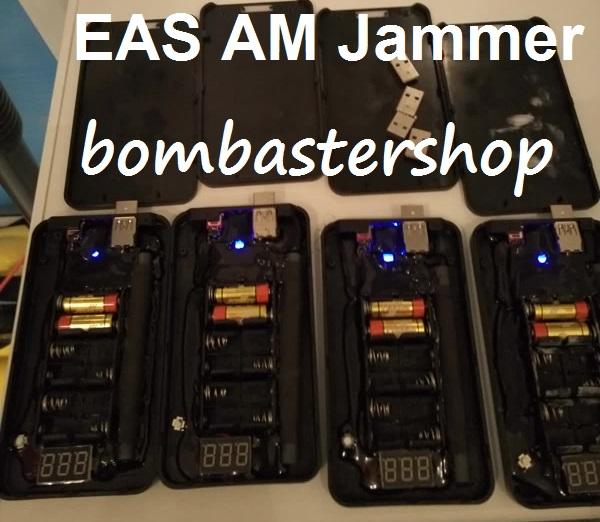
A seller nicknamed Medved (Bear) appeared on one of the forums. He rolled out "incredible" AM and RF jammers. In reality, it was the exact same ancient Danko technology (from the Belarusian), shoved into new black plastic boxes with a power switch.
The technology could not withstand any scrutiny. But Medved monopolized the forum thread: generously handing out promises, filming laughable home videos with the dumbest EAS gates, and ruthlessly deleting any negative reviews. People bought this trash.
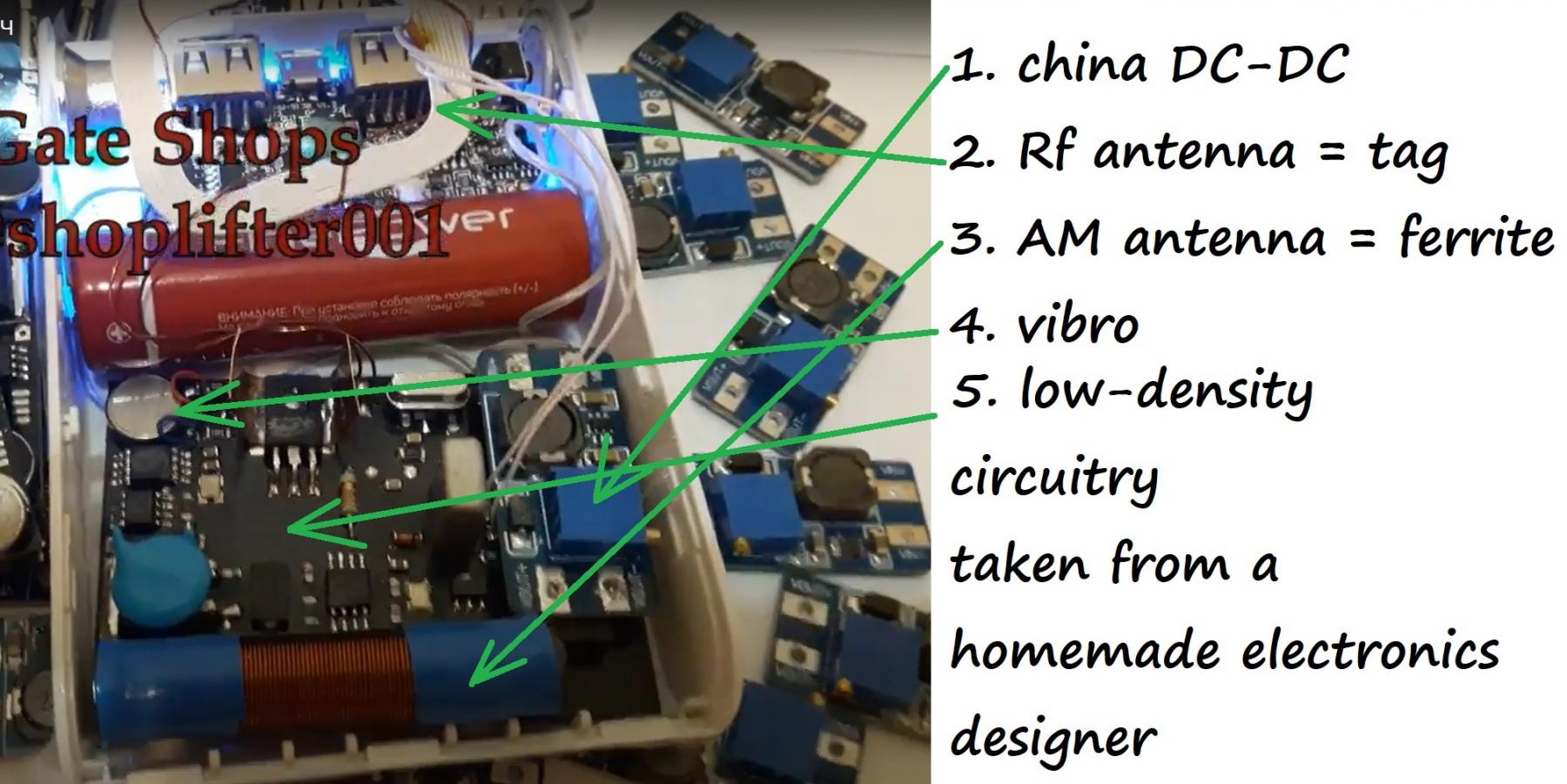
Subsequently, 2 years later, he stole my idea of power bank camouflage, but truthfully failed to engineer any control system or competent mode switching, since he was never an actual developer. Another 2 years passed, and he exited this market, selling these technologies to yet another "new manufacturer" from Russia, who also began promising miracles. But all he managed to do was rip off my idea for vibro-indication of the device's operation. The real effectiveness did not change, nor did the internal antenna emitters (instead of an antenna for the RF jammer, they use an RF hard tag, which was originally designed solely to receive a signal, not to emit one). I saw absolutely zero progress from these miracle workers; this both amused and saddened me, as I had dreamed for a long time of a competitor who would invent something conceptually new and high-quality.
Ultimately, the third generation of 2011 tech sellers ceased to exist in March 2020 by defrauding one of their buyers. The seller shoplifter001 secured 1000 euros (reports say there were many more) and vanished. What is unique to all these sellers and all my competitors is that they are perpetually terrified of direct contact with buyers. Not a single one of them was an operator, and none ever understood what it means to risk your freedom and your fate. This is exactly why such sellers peddle devices they refuse to take responsibility for. To them, we are nothing but a cash cow.
The iPhone 4 Illusion (2014)
Around 2014, nevertheless, a small miracle occurred. The developer from Yaroslavl returned to the game briefly and managed to build a unique AM jammer camouflaged as an iPhone 4 replica. For me, this was a breath of hope; I started hunting for contacts to reach him again, but he vanished once more. I only managed to dig up intel that he was an employee at a major computer electronics engineering firm, treating this as a temporary hobby for a friend. Securing this miraculous iPhone and comparing its performance against my hardware, we were somewhat disappointed... The power output was pathetic due to the form factor and antenna size. Out of 7 algorithms, almost all were useless, but it was a solid piece of craftsmanship, and I keep it safe in my museum. As history has shown, legends, when subjected to reality checks, most often turn out to be exactly that — legends and attempts to fabricate an illusion of supremacy.
Engineering Breakthrough and the Era of Algorithms (2015–2019)
So what had we achieved since 2012?
By 2015, all my devices were sold with camouflage, became compact and stable, but I had not yet sold RF jammers publicly since their reliability was limited and did not meet my strict parameters. I sold them only to close associates with highly detailed manuals.
New pedestals with built-in metal detectors were reverse-engineered — gates that emerged and were entirely immune to basic bypass methods. Several algorithms for specialized jamming and disrupting gate logic were engineered.
In 2016, we migrated to a new class of processors and began integrating smart control systems for the jammers, engineering a locking system and vibro-feedback. Following this, all hardware we manufactured was sold exclusively in POWERBANK camouflage. Effectively, in 2016, we made the decision to reinvent our jamming methods and hardware architecture every single year from scratch, integrating newly acquired skills, knowledge, and field experience. This catalyzed the rapid evolution of RF system defeat protocols. As a result, in 2018, I launched an RF jammer I could be genuinely proud of, without the fear of destroying my reputation through sales. A year later, we optimized it further, engineering a "2-in-1" unit vastly superior to anything I could have dreamed of back in 2015.
That same year, we locked in a strategic protocol: reinvent jamming methods and circuitry annually. Never rest on legacy achievements, but rewrite the code leveraging fresh intel.
Our Own CNC Machine: Speed vs. Mass Production
To accelerate R&D, we mastered CNC technology and assembled our own high-precision rig for milling circuit boards.
"Specialists" frequently ask me: "Why don't you order boards in batches of thousands from factories in China? It's cheaper!"
My answer: Mass factory production is absolute evil in our sector. By ordering a batch of 1000 boards, you become a hostage to legacy technology until you sell every last one. Our in-house CNC rig allows us to alter board architecture on the fly. If an idea hits us tomorrow, the day after tomorrow we have a working prototype and a validated hypothesis. You always receive the bleeding-edge tech, not two-year-old warehouse deadstock.
This CNC machine, built with our own hands using capital from sales, unlocked unprecedented capabilities for experimentation.
Antenna Physics: Why We Abandoned Ferrite
We acquired our core knowledge by exhaustively analyzing antenna behavior at target frequencies. Today, we know more about the physics of emitters than some engineers employed by EAS companies.
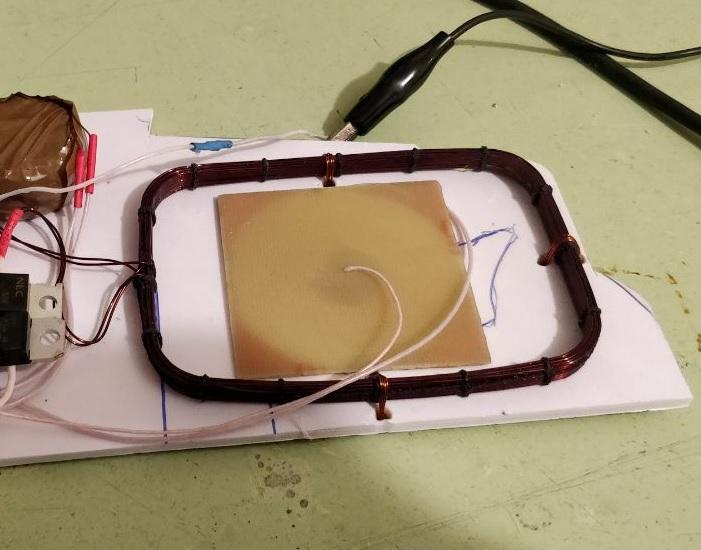
Our emitters are conceptually distinct from the junk pushed by "competitors." The Chinese and garage hackers use ferrite rod antennas for AM jammers. The critical flaw of ferrite is that it generates an excessively uneven, "fragmented" emission field. We migrated to a complex winding technology for loop antennas, which generate a dense and uniform field.
Regarding RF systems: during R&D, we realized that the developers of modern RF gates had begun utilizing a tag detection logic highly comparable to AM technology. This intel was a breakthrough. In 2018, we launched an RF jammer I could genuinely take pride in. A year later, we fused it all together, creating a "2-in-1" device with a level of quality I couldn't even dream of in 2015.
The Zoo of New EAS Technologies
While we were advancing our hardware, the gate manufacturers (Sensormatic, CrossPoint, Nedap, Gateway) weren't sitting idle. Plunging electronics costs allowed them to integrate high-power processors (DSP) directly into the pedestals.
EAS gates learned to analyze the signal. Primitive "white noise" was dead. A zoo of technologies emerged, where each brand deployed custom defense protocols:
- Sensormatic Synergy: Learned to dynamically alter analysis algorithms in real-time. Legacy jammers caused them to either hard-freeze or trigger a false alarm (Anti-Jammer).
- CrossPoint (Netherlands): Deployed digital adaptation technology. Upon detecting interference, the gates don't go "blind"; they recalibrate, mathematically subtracting the jammer's noise from the spectrum.
- Nedap (RF): Learned to differentiate the signal of a genuine radio tag from a jammer's signal by analyzing the waveform.
It is impossible to engineer a single signal that deceives all manufacturers simultaneously. This is exactly why a professional device evolved from a noise generator into a complex computer equipped with an arsenal of "digital skeleton keys."
- Mode #1: The classic algorithm, upgraded with our proprietary modifications.
- Mode #4: A specific key engineered to bypass CrossPoint filters.
- Mode #7: A precision electronic screwdriver for Sensormatic Synergy.
And what happened in the realm of my "competitors" by 2018, oops, I mean 2020? Absolutely nothing))) Zero. Nobody invented a damn thing, nobody started selling anything conceptually new or remotely functional. In my view, I was left entirely alone on the battlefield. Not a single one managed to defeat CROSSPOINT systems even slightly; nobody could handle Synergy tech or engineer an RF jammer with the power output required to crush Chinese RF systems, LUCATRON, or the latest RF CROSSPOINT pedestals.
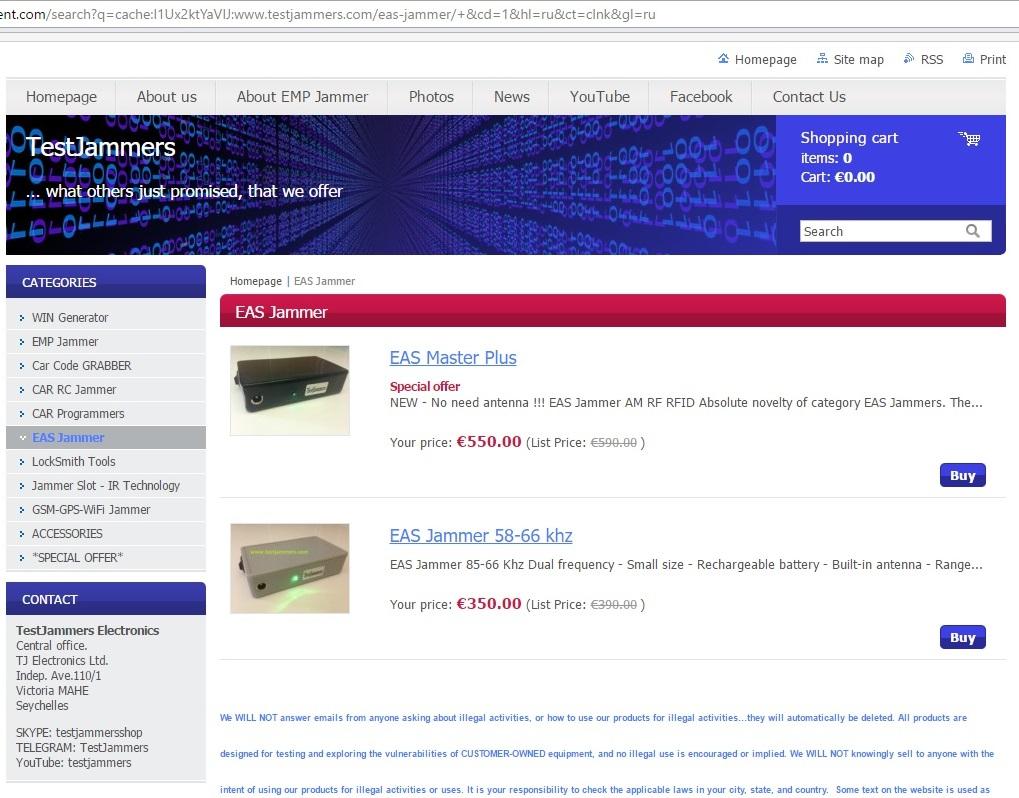
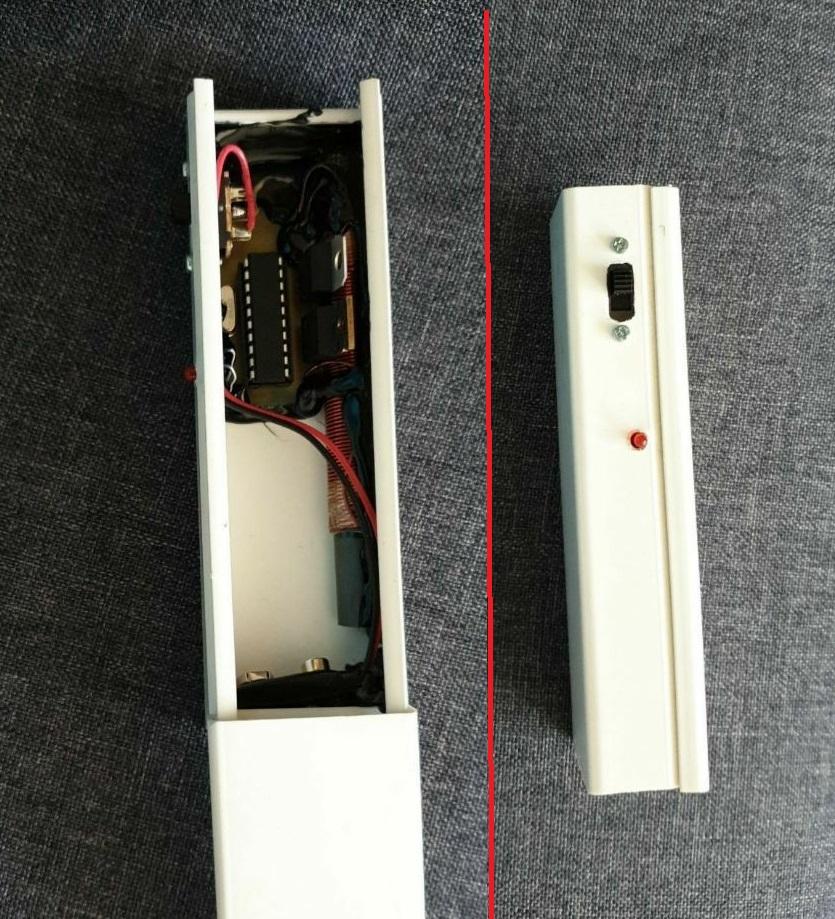
The Bulgarian, as we discovered in 2014, sold all his tech to Germany, and the Germans later flipped it to Croatia. http://easblocker.com
What are the Croatians doing now? They tried to upgrade it, but only made it worse. They buried the external antenna inside the chassis, crippling the transmission radius, which was the single advantage of that unit. Today, it is a dangerously obsolete device across the board, incapable of defeating modern systems. A rig with toggles and LEDs that almost any security guard in Europe will instantly recognize, as its photos have been floating on Google for years. They drastically slashed their prices, but they remain stuck in the dark ages.
In 2015-2016, a soldering-iron enthusiast on a forum built an interesting rig inside a radio receiver. It was almost functional, but the circuitry looked like absolute hardcore gore — as if it was assembled at the dawn of the electronic PCB era using medieval tools.
One of the Polish guys is still slowly trying to peddle his fake 2-in-1 jammer replica (see the beginning of the article). Another one recently figured out how to hide this same "2-in-1" rig inside a power bank, but failed to engineer a high-power converter and amplifier. It remains more of a fake than a jammer, demonstrated in living rooms against obsolete junk with the pedestal sensitivity dialed down to absolute minimum: https://www.instagram.com/p/B3UM_q2Bt8N
Reminder: all of them operate anonymously. Nobody will disclose their location or name; we only know rough addresses and seller profiles based on reports from defrauded buyers.
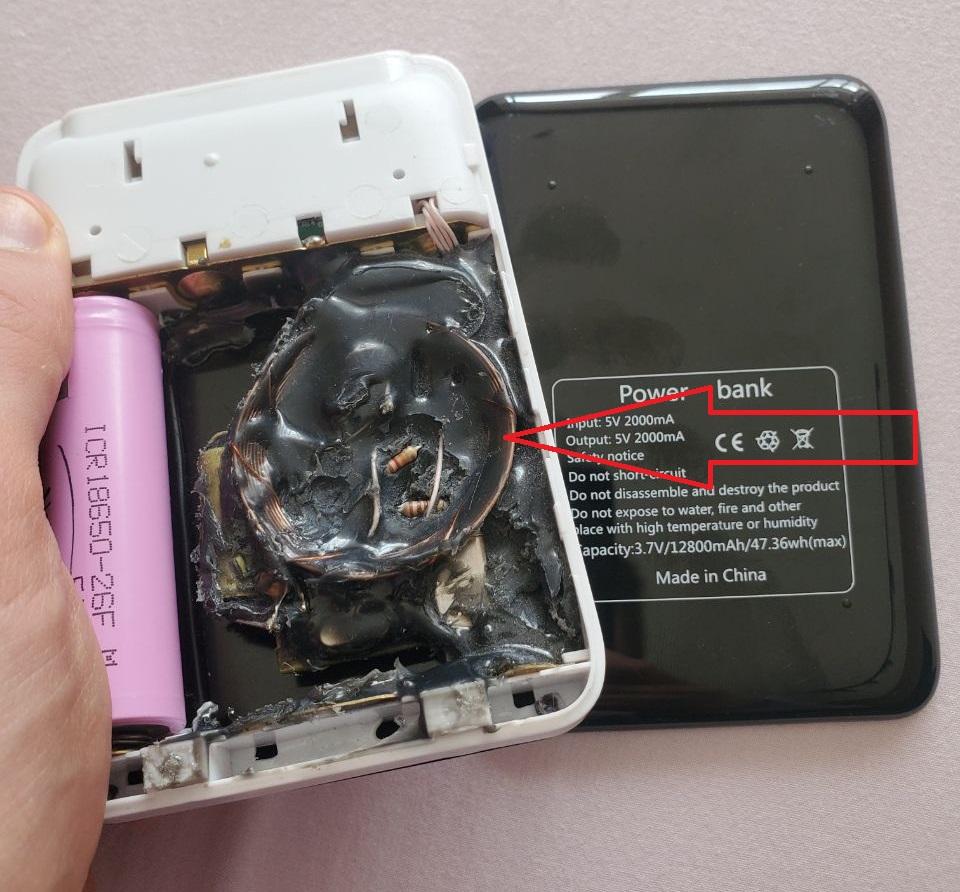
The operator of Testjammers (https://www.testjammers.com) spent years flipping one device after another, and has now returned to reselling the Super Multi Jammer from 2010... But eventually, he stooped to selling fake jammers imported from China. Just imagine the sheer audacity of vendors on supposedly "serious" platforms:
The Scam Protocol: Advertise miraculous capabilities, secure the buyer's funds, and pay a Chinese supplier for a fake device worth 10 times less. In the end, you receive a package not from Europe, where you sent your money, but FROM CHINA.
This hardware generates a microscopic signal on the 58 kHz frequency, and does absolutely nothing on 8.2 MHz... And the seller will not refund your money. Period. Denied.
Here is the magical box the Chinese claim can do it all)))
https://hgjammer.com/product/en/EAS-Master-Plus-EAS-Jammer-.html
What a miracle, jamming all frequencies simultaneously using a micro-battery and a single antenna engineered to emit a microscopic AM signal. And by pressing an RF tag against this antenna, shoving the lock protrusion into a hole, the Chinese vendor "proved" it jams RF too (this only works due to the physics of the RF sensor itself, you already understand shielding).
The Chinese supplier sells this garbage for $180... https://www.dhgate.com/product/supermarket-eas-anti-alarm-generator/387597006.html
There is only one review, but it reflects grim reality. I pity the buyer.
It is infuriating for everyone who grinds and risks their freedom to secure funds for hardware, only to buy this shit from these hustlers and lose their money.
That wraps up everything that occurred over the last few years. Today, we continue to grind, experiment, and reinvest a massive % of our revenue directly into R&D and field testing.
How We Rewrote the Rules Again (2024–...):
By 2023, we hit a ceiling. The technologies we engineered became too complex for a single button. When you have an arsenal of ten algorithms for distinct tactical situations, "blind" tactile operation stops being an advantage and becomes a bottleneck (!critical clarification: for some inexperienced operators).
We realized: something had to change, we needed to shift gears, recalculate the vectors, it was time... And, as always, we delivered.
Back in 2014-2015, we were the first to conceal electronics inside a PowerBank chassis. A couple of years later, everyone started doing it — from garage hackers to Chinese factories. They simply copy-pasted the concept because it became the industry standard.
ALTERING THE LANDSCAPE (2025-2026)
We executed the next maneuver, one that will invert the market for the next decade. We stripped away physical controls and migrated everything into a stealth web interface on a smartphone. This isn't just a "remote control on a screen." This is absolute command supremacy.
Lock this moment into your memory. Give it a year or two, and you will watch our "competitors" start cobbling together their crooked apps and web interfaces. They will try to mimic us again, selling you a pretty picture on a screen. They will copy the menus, they will rip off the buttons, but they will never replicate what powers that interface.
Why We Will Remain the Only Ones
The migration to digital gave us something the fly-by-night vendors lack and will never possess: response velocity. In the past, to patch a device against a new EAS update, we had to bounce packages across international borders. Today, the device is a living organism.
We engineered the "Engineering Menu" and open architecture not for flexing. We did it because we actually listen to you. We are the sole entity in this market that hasn't walled itself off from operators behind a "tech support" barrier. We operate on your exact frequency. When a guy from another country hits us up: "Boys, there are new pedestals here, your modes aren't cracking them," — we don't ghost him. We work with him, via that exact menu, to brute-force the keys. And the millisecond a solution is locked in, it is deployed to everyone.
Money Does Not Divide Us
The ultimate secret to our longevity (15 years is an eternity in our sector) is not found in transistors or source code. The secret is that we haven't launched into orbit on our own ego. We haven't mutated into a faceless corporation that exists solely to clip coupons.
The intel you feed us, your debriefings, your successful extractions, and your critical failures — that is the fuel for our evolution. We remain high-initiative extremists who simply want to forge the absolute perfect tool. The capital we secure is nothing but ammunition, allowing us to acquire new CNC rigs, run new hypotheses, and stay on the grid 24/7.
Competitors will spawn and die. They will clone our chassis, plagiarize our intel, and attempt to spoof our interfaces. But they will never, ever spoof the secure channel that exists between us and our network.
The history of jammers is not a history of "hardware." It is the history of operators who refused to accept limits and chose to dictate their own terms to reality.
We keep grinding. We keep hunting. And we are always on comms.
2009 - 202...













.jpg)














.jpg)