RFID SYSTEMS
RFID has finally landed in our AO. Intimidating- Not in the slightest.
- I’ll start with the good news: avoidance is simple. Briefing over-
For the tactical minds looking ahead, let’s continue...
Stripped of the fluff marketing "experts" love to bury it in. Let's go:
1. Technical Architecture
RFID is merely a catch-all term for a specific data-retrieval protocol. A tag consists of:
An antenna, a capacitor, and a CHIP containing pre-programmed Intel.
If we remove the CHIP from the circuit of a 13.56 MHz tag, guess what we get- A standard-looking RF tag. Why- The physics of interrogation for 8.2 MHz and 13.56 MHz tags are functionally identical.
RFID Frequencies and Tag Classifications:
- 125–134 kHz - Used exclusively for proximity contact reading. Range is extremely limited.
- 13.56 MHz - Used in access control pedestals or for inventory scanning, but range is capped at 1 meter for reliable data retrieval.
- 860–928 MHz UHF - OUR primary concern. Utilizing specialized antennas at ultra-high frequencies, interrogation is stable up to 3 meters.
- 2.45 + 5.7 GHz - Currently not mass-deployed in retail. A more specialized system for long-range asset tracking.
Why was UHF (Ultra-High Frequency) chosen-
The ratio of system cost / tag price / interrogation range.
Options 1 and 2 fail due to poor range. Option 4 is cost-prohibitive for mass retail, though that may change in the distant future.
In comparison, AM (Acousto-Magnetic) and RF (Radio Frequency) EAS systems also use tags but operate in different dimensions.
AM systems run at roughly 58 kHz, while RF systems run at 8.2 MHz.
These lower frequencies allow AM and RF tags to remain simple-they lack a data chip and rely on a resonance circuit.
However, this limits their interrogation range compared to RFID tags operating at higher frequencies.
2. Tag Morphology
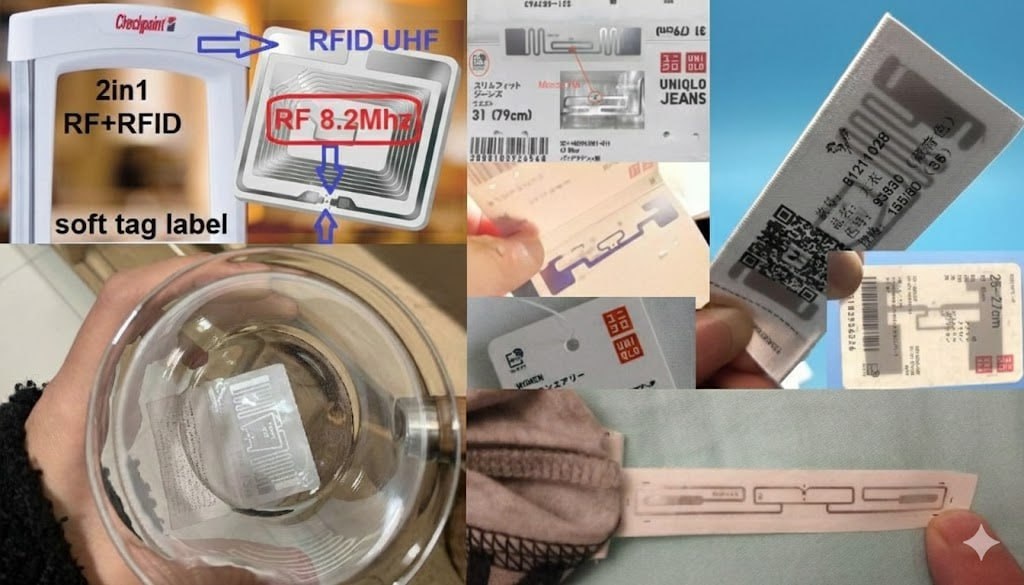
1) Soft Tags and Adhesive Labels
Morphology:
Dual-antenna configuration usually 2×5 cm, sometimes smaller, but the length is standard;
Combined RFID+RF dual-antenna square, 4×4 cm;
Other configurations fail at this frequency due to energy transfer limitations. High-turn coils do not function at UHF; spirals are for RF and 13.56 MHz access systems.
Readers interrogate tags not just in the checkpoint area (entry/exit) but significantly further to the sides.
Signal analysis algorithms can triangulate a tag's location with high precision. This works because the tag has two antennas, and readers are calibrated specifically for the tag types used within that store or chain.
2) Hard Tags with Integrated RFID
Morphology:
- Frequently engraved with the "RFID" logo;
That's it... in some cases, you won't distinguish them from AM or RF visually without knowing the inventory. Here is Intel from our field database.
Key Iterations:
1. Sensormatic 2-in-1: Grey SuperTags with integrated RFID deployed before 2010 (AM coil + thin flat RFID inlay);
2. CheckPoint 2-in-1: Standard RF tag with a circular RFID inlay, seen around early 2010;
3. Third-party manufacturers: Rapidly scaling production to fill the market vacuum.
Crucial Detail: Every hard tag from a specific manufacturer typically shares... the exact same tag code. Logically, they are flagged simply as a SECURITY TAG.
They are not unique identifiers and carry zero data about the item they protect!
.... The beauty of this is that if you run a small shop and you’re sick of EAS gates, you can... just install an RFID system, swap the tags, and you're done. No complex software infrastructure required. Just tell the reader that this specific RFID code means TAG... mission accomplished.
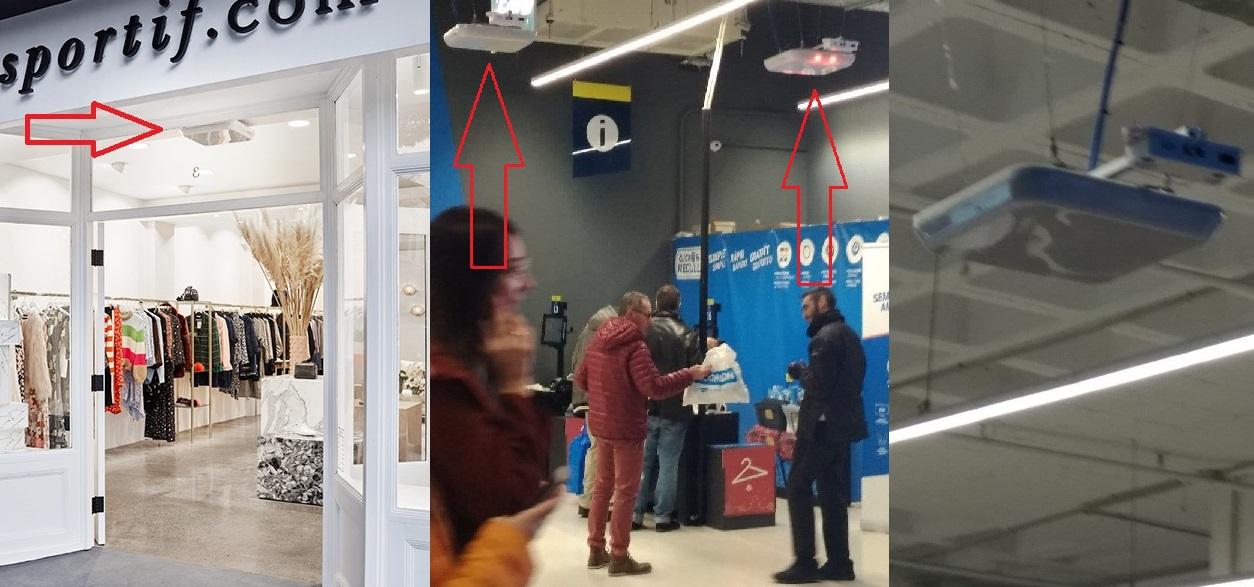
3. Identification of RFID Readers
!!! Operators: Pay attention. You will notice that reader designs vary by manufacturer, much like AM or RF pedestals !!!
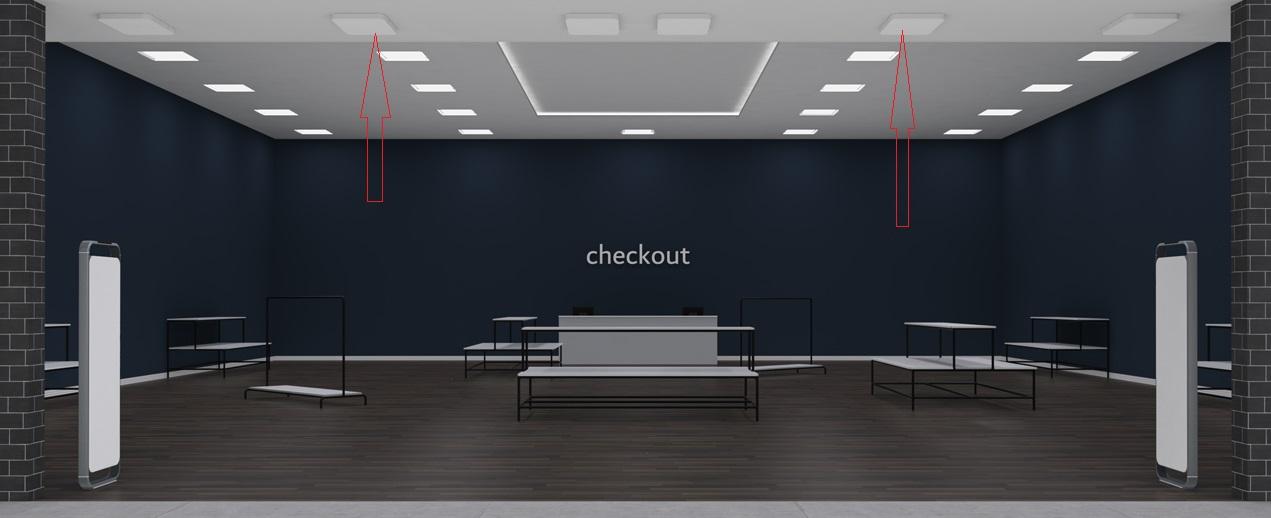
OVERHEAD MODELS
NEDAP - Rounded forms, integrated point LEDs (the unit with two "black eyes" is a visitor counter, ignore it):
Sensormatic - Rectangular design mirroring the aesthetic of the latest AM Synergy pedestals:
Zara and Inditex - Currently augmenting AM systems with RFID panels globally. Manufacturer unknown, but likely proprietary Inditex tech:
Checkpoint - Highly distinct. Recognized by the two-part main antenna and auxiliary antennas designed to eliminate blind spots:
INTEGRATED GATE MODULES
NEDAP - Offers a dedicated line of pedestals with an RFID module appearing as an expanded mid-section. Development has continued into the newest series:
Sensormatic - Provides RetroFit modules (augmenting AM) that mount directly onto the Synergy AM pedestals, covering the frame's surface area:
Checkpoint - Developed modules that install directly onto or inside existing gate frames (seen in Decathlon "box" pedestals, UNIQLO, and other budget-conscious upgrades):
The latest innovation from Checkpoint is the SFERO model-a complex system combining two powerful lateral readers with overhead modules. Promotional Intel below:
Checkpoint SFERO Reveal
4. Vulnerabilities
Field testing shows RFID tags aren't easily neutralized by basic physical trauma. Review the video: you must isolate the chip from BOTH antennas; otherwise, you merely reduce interrogation range without deactivating the tag.
Debriefing the Intel:
Do I need two cuts near the chip-
- Inspect tag photos. Cutting the tag across its center line will definitively sever the contact between the chip and the antennae.
What happens if the cut is imprecise-
- Interrogation range drops. This might allow passage through overhead readers, as their range is inherently smaller.
Why show initial cuts far from the chip-
- To demonstrate the tag's resilience to minor surface damage.
RFID WEAKNESSES:
- Like RF, tags fail if placed against metal. Waves do not penetrate metal. Reading requires direct line-of-sight or radio-transparent obstacles (the merchandise itself);
- Vulnerability to precision physical trauma.
That’s it...
These two factors effectively nullify any chance of RFID completely replacing other EAS systems.
That was our assessment in 2021. The world moves faster now. RFID dominance is an inevitable reality.
Our Countermeasures:
1. RFID tag scouter: Locates tags for physical removal or deactivation. Prototypes complete; pending release alongside the jammer;
2. RFID tag deactivator: Development scheduled for 2024;
3. Our specialty-Jammers. Currently in development (first public prototype tested Feb 15). Release expected Summer 2024.
The jammer will initially be sold as a standalone unit. Future iterations may integrate it with AM/RF hardware, but that's a separate engineering track.
WATCH THE PROTOTYPE DEMONSTRATION:
WHAT ABOUT FOIL--- They can't install Metal Detectors against foil, so back to the past!!!
- Negative. AM, RF, and RFID frequencies exist in different universes. RFID propagates around obstacles effectively. Your only options are a steel pot with a lid or extremely tight foil wrapping.
I tried to write an explanation, but field tests were more conclusive. Even with a high-grade foil bag, if the tags aren't at the very bottom, they are vulnerable. A HANDHELD interrogator can read tags from 3 meters away from the bag’s side. Overhead systems will look right into it.
See for yourself:
5. Industry Trajectory
Since our 2021 briefing, the entire INDITEX network (Zara, Bershka, etc.) has fully integrated RFID-both overhead and as pedestal add-ons.
The deployment was rapid; within months, field reports of active systems arrived from every territory.
INDITEX utilized RFID for logistics and inventory tracking for years, but held back on EAS implementation until recently.
Tag Placement in INDITEX Merchandise:
- Beneath the sewn-in branding labels (size labels);
- Inside the care/washing instruction tags;
- Integrated into AM SuperTags (long-standing practice).
Notably, Checkpoint predicted this 10 years ago on their YouTube channel, showcasing RFID interrogation at the security gate level. See for yourself:
Checkpoint RFID Vision
Initial barriers were high equipment costs and a lack of qualified technicians for precise calibration. Over time, production scaled, costs dropped, and Chinese manufacturers flooded the market with cheap tags.
RFID is now embedded in almost every commodity-you’ve seen it over the last 5 years. The field is wide open for EAS application.
Grocery hypermarkets will likely be the last to switch, as the cost for low-margin consumer goods remains prohibitive for now.
What was missed-
- RFID isn't just hardware... it requires expensive software, computing power, and comprehensive logistics management from factory to consumer. Without this, the ROI fails. You can study the commercial motives for integration here:
RFID System Logic (RU Source)
Predicted Early Adopters (AM/RF Phase-out):
- H&M: Installing exclusively RFID-integrated NEDAP pedestals in all new locations;
- ADIDAS and NIKE: Long-standing use of factory-applied RFID and warehouse interrogators;
- JD Sports: Active implementation in select regions;
- Celine, CK, Marc O'Polo, Etam... the list is growing.
Adidas promotional Intel on RFID deployment (partnered with EU-based NEDAP):
Adidas & Nedap RFID Case Study
Small local retailers aren't attempting integration yet.
!!! HOWEVER... once the mass-market giants fully transition, a surplus of specialized technicians will flood the market, and security firms will aggressively market RFID to smaller boutiques.
Observations: AM and RF systems have hit their technological ceiling. Development has stalled, signaling the "end-game" for these protocols. RFID also provides global analytics on goods and PEOPLE. An RFID tag from one store can be read by any reader, anywhere. If databases start merging, your movements could be tracked far more precisely than by your phone alone...
6. Practical Field Intel: Shoplifter vs. Security
Every unsold item has a unique chip code (factory serial number).
When you enter an interrogation zone with an active tag, the guard’s specialized smartphone receives a notification: "Item [X] is in Zone [Y]." The guard will approach and ask, "Busted-)"...
Actually, they’ll ask about the item, then scan you with a handheld interrogator to pinpoint the tag.
These handheld units are currently expensive, but they are becoming common equipment.
If the item was purchased, the RFID code is logged at the POS and flagged as "paid." Passing through readers with it will display the departure in the database, but won't trigger an alarm on the guard's phone.
Strategic Applications:
- How you utilize this Intel is up to your imagination. I won't provide specific tactical instructions; you already know what to do.